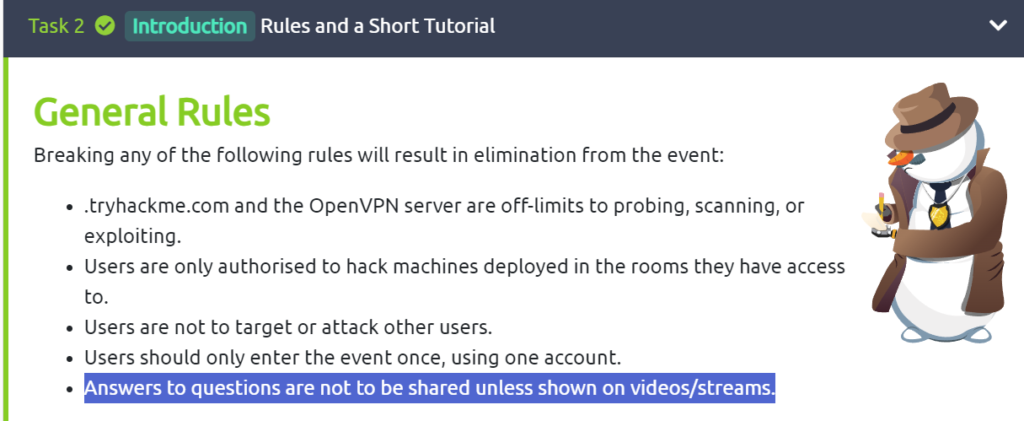
I’m a rule follower, so I can’t write up the walkthrough for this TryHackMe room. This one will be a video. Click play above to follow along.
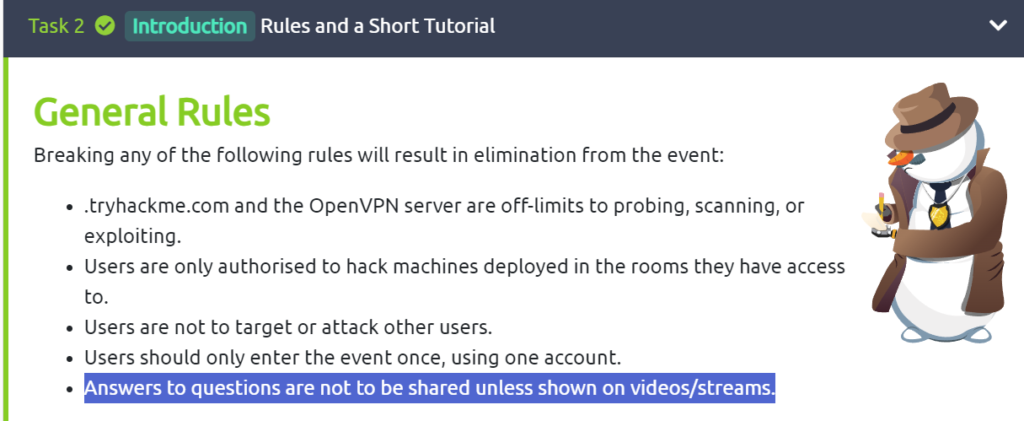
I’m a rule follower, so I can’t write up the walkthrough for this TryHackMe room. This one will be a video. Click play above to follow along.
Preparation is the first room in the Incident Response learning path within the TryHackMe learning platform.
The learning path consist of the following rooms:
In this post I will be walking through Identification & Scoping.
Question 1: No answer needed.
Question 1: What is the Subject of Ticket#2023012398704232?
Follow the directions in the reading to dismiss all the Windows Office warnings. Once outlook opens on the VM scroll down the inbox to the first message from John Sterling that’s the one with the correct ticket number from the question. In the message thread scroll to the first message and you will see the ticket information including the subject.

Answer: weird error in outlook
(more…)Preparation is the first room in the Incident Response learning path within the TryHackMe learning platform.
The learning path consist of the following rooms:
In this post I will walkthrough the Preparation room.
Question 1: No answer needed
Question 1: What is an observed occurrence within a system?
The answer is in the reading. Look at the first bullets in this task.
Answer: Event
Question 2: What is described as a violation of security policies and practices?
This answer is also in the reading, in the same place as question 1.
Answer: Incident
(more…)In this post I’d like to talk a bit about TryHackMe and my experience working through the SOC Level 1 learning path.
TryHackMe is a learning platform that sends users to virtual machines (VM) they can access through their web browser. Extremely low barrier to entry! Absolutely no previous knowledge is required. I’m not sponsored and TryHackMe did not ask me to write this.
I’m a big fan of theirs. I think the learning paths and rooms (think learning modules) are fantastic hands-on learnings! I learned
Each room walks the learner through hands-on learning. I learned all these tools:
And even more! It’s a great platform. As of this writing it is $14 a month. If you’re not going to use it, don’t sign up, but if you really want to learn these tools and more it’s a great place to get started. You can spend as much time as you want learning these tools in real environments. You can’t break anything because it’s all VMs that start fresh each time the are launched. Getting the chance to work on these environments without setting up all these VMs is a huge time savings.
If you want to play around in there for free you can do that too. There is plenty of free content to get started with and see if you want to pay for the premium rooms and features. It’s worth checking out.
Only one task for this room.
Question 1: What date was the email received? (answer format: M/DD/YY)
I opened the email in Thunderbird.
Answer: 6/10/20
Question 2: Who is the email from?
In the From…
Answer: Mr. James Jackson
Question 3: What is his email address?
Also in the From…
Answer: info@mutawamarine.com
(more…)Question 1: After visiting the link in the task, what is the MITRE ID for the “Software Configuration” mitigation technique?
Follow the link to https://attack.mitre.org/techniques/T1598/#mitigations. Look for Software Configuration and the ID is there.
Answer: M1054
Question 1: Referencing the dmarcian SPF syntax table, what prefix character can be added to the “all” mechanism to ensure a “softfail” result?
Follow the link to the page and then click on the here in: “More in-depth information on the differences between “~” and “–” can be found here“
This gives you the…
Anwser: ~
Question 2: What is the meaning of the -all tag?
This answer is on that second webpage as well. Scroll down a little and to see the difference between ~all and -all.
- “softfail” in the case of “~”
- “fail” in the case of “-“
Answer: fail
(more…)Question 1: No answer needed
Question 1: No answer needed
Question 1: What is the official site name of the bank that capitai-one.com tried to resemble?
This should be self-explanatory, google capitol one to see what their domain is.
Answer: capitalone.com
(more…)Question 1: No answer needed
Question 1: What phrase does the gibberish sender email start with?
This answer is in the reading. Look at the email address highlighted with a red circle 2.
Answer: noreply
(more…)Question 1: No answer needed.
Question 1: Email dates back to what time frame?
Answer is in the reading. Second paragraph.
Answer: 1970s
(more…)In this walkthrough we will go step by step to answer the questions.
No questions here, so let’s keep moving.
Question: Which team uses malware analysis to look for IOCs and hunt for malware in a network?
The answer can be found in the reading in “The purpose behind Malware Analysis” section. Specifically, the Threat Hunt bullet.
Threat Hunt teams analyze malware to identify IOCs, which they use to hunt for malware in a network.
Answer: threat hunt teams
(more…)